I combine law-enforcement OSINT expertise, offensive pentesting training, and extensive criminal intelligence to find and fix what others miss for your digital security posture.
PACKAGES AVAILABLE
-

FOUNDATION
This package is best for clients who want a full, one-time clean-up and an actionable roadmap for cyber best practices.
KEY INCLUSIONS:
· Deep OSINT on principal, staff, family, and residences
· Full data-broker removal & real estate removal (50+ sites)
· Dark-web and breach scans for compromised personal information
· Credential impersonation and review
· Home IoT/smart-device audit
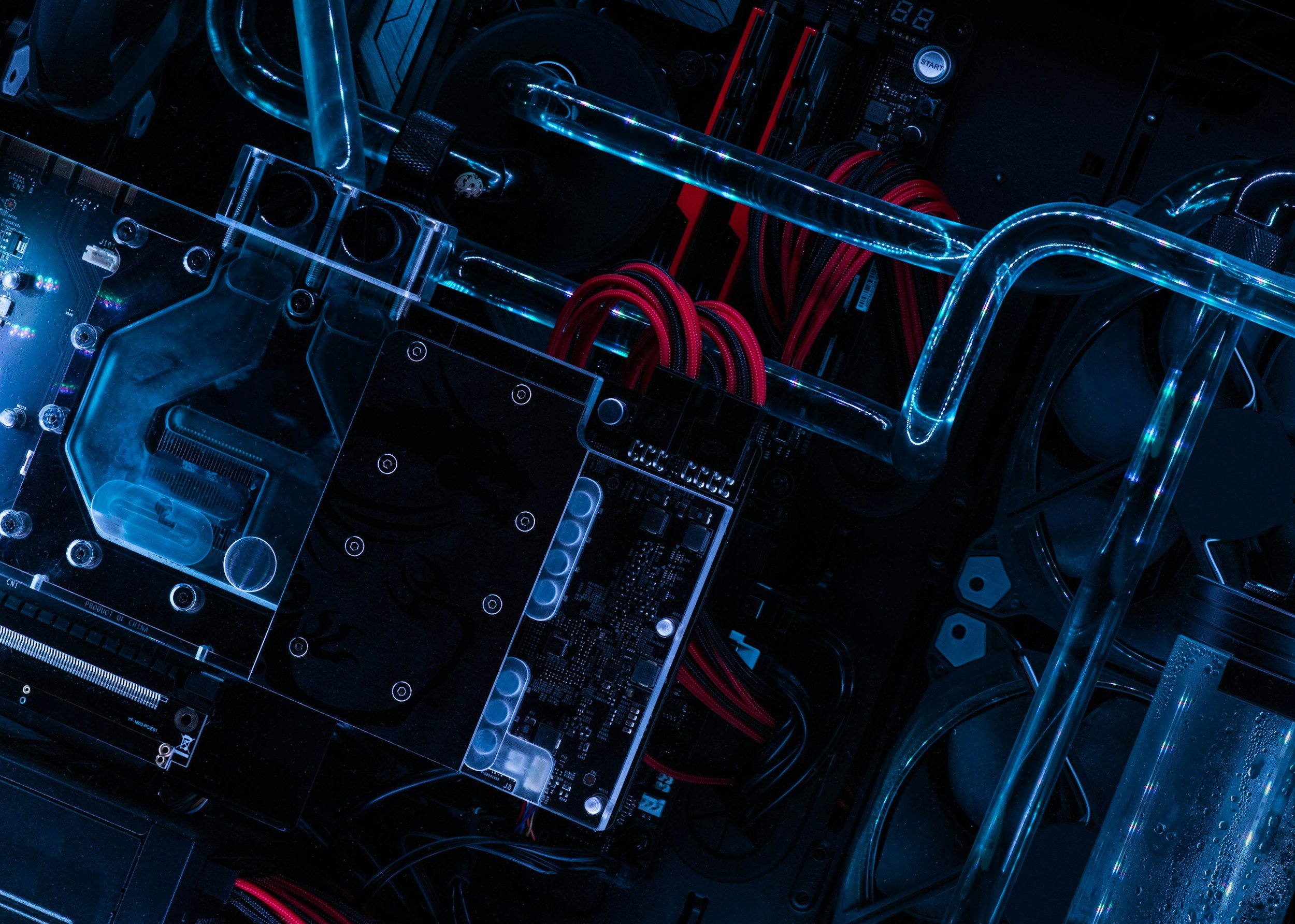
· Home network penetration test (one full test included)
· Best for hardening home networks against intrusion and compromise
· Detailed remediation playbook + 30-day follow-up validation
-

PROTECT
This package is best for clients who have heavy travel schedules, past incidents, or rising public profiles.
KEY INCLUSIONS:
· Everything in Foundation plus:
· Continuous breach and dark web monitoring with real-time alerts
· Quarterly exposure re-scans and re-removals
· Pre-travel digital risk briefs
· Impersonation and doxxing takedown service
· Priority response (< 4 hours initial contact)
· Monthly threat briefings for security team
-

ELITE
This package is best for high-profile athletes, high net worth families, or principals with known targeting concerns
KEY INCLUSIONS:
· Everything in Protect plus:
· Two full home-network/business network and IoT penetration tests per year
· Ongoing smart-home device hardening and firmware management
· Optional Mobile Device Management (MDM)
· 24/7 Incident Response (< 2-hour callback, < 24-hour containment)
· Annual criminal intelligence deep-dive
What We Do
-
I am a certified ethical hacker capable of uncovering your vulnerabilities before adversaries do. Testing is tailored to the client’s unique digital environment—ranging from home automation systems and Wi-Fi networks to employee portals and third-party applications. Findings are documented in executive-level and technical reports, prioritized by risk and remediation effort.
-
I use advanced OSINT methods to identify, map, and mitigate publicly available information that can be weaponized against high-profile individuals and organizations. This includes locating exposed personal data, metadata leaks, and digital footprints across social, open, and dark web sources. Are your employees’ email accounts and passwords for sale on the dark web?
-
I assess and harden the technology environments surrounding the principal—home, travel, and mobile. This includes evaluating smart-home systems, routers, mobile devices, and employee endpoints for misconfigurations or data-leakage risks.

